JALANDHAR, Punjab — Online classified ads company Sulekha’s ‘convenience’ feature, which allowed millions of customers to auto-login into their accounts, enabled a glaring security flaw which may have put user data and the money in their linked prepaid wallets at risk.
The company removed the option immediately after HuffPost India alerted it on March 13 this year.
More than 5.5 lakh businesses have registered accounts with Sulekha to advertise their services to customers, and many of these have linked prepaid wallets containing lakhs of rupees to their accounts to ease their transaction speed.
When a user searches for a product on Sulekha, advertisers belonging to the category get an SMS alert with a seven-character alpha-numeric code. On entering this code into the Sulekha website automatically logs the user into their account.
Changing the digits of the code, however, logged you into a different account. By rearranging the characters randomly, you would be logged into a completely different account, and anyone with basic computer skills could have used this access to create a program to work through a series of characters, and built a database of advertisers and associated codes.
Once inside another advertiser’s account, it was possible to change the name and add new phone numbers, as well as access the money stored in the digital wallet, without the actual advertiser knowing about this.
The person could also edit, add, delete or replace any of the services offered by the advertiser with his/ her own, view the contact number of the lead purchased by the advertiser, and access the chats with all the leads.
Srini Vasan, Chief Technology Officer of Sulekha, said the feature, which had been added after receiving numerous requests from service providers, had been especially helpful to small-time vendors who often changed their mobile numbers.
However, Palvinder Singh, a Jalandhar based cyber security expert who found the bug, said the flaw was a serious one as none of the changes made through the ‘auto-login’ option was OTP-driven and advertisers did not receive SMSes informing them about any changes made to their accounts.
Sulekha is not the first (or last) Indian company to take a lax approach to data security. In September, HaveIBeenPwned.com revealed that a data breach on food-ordering service FreshMenu had compromised data of 100,000 users. In 2017, hackers stole data of 17 million Zomato customers, and HuffPost India found earlier this year that India’s biggest diamond traders, who take the physical security of their inventory very seriously, were happily unaware that they were leaking information about customers and transactions onto the open Internet.
What’s also common between all these companies is that they did not follow policies of responsible disclosure, and did not respond to security researchers who first brought the problem to their notice.
No passwords, no OTPs, no security
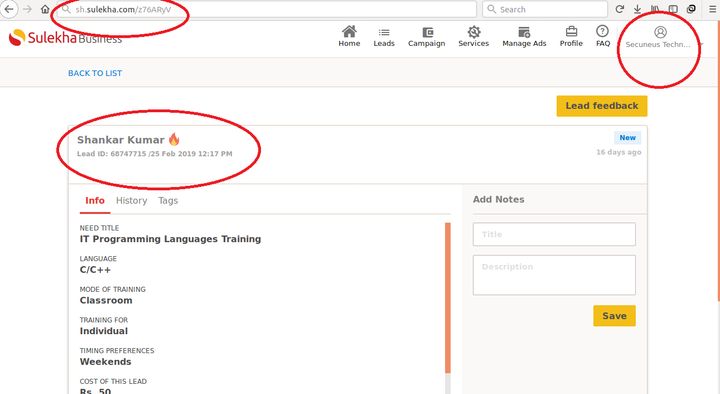
Singh, CEO of Secuneus Technologies Pvt. Ltd, a Jalandhar-based cyber security training institute registered with Sulekha, first noticed the problem in December 2018. After discovering the bug, Singh sent an email to Satya Prabhakar, Sulekha’s founder and CEO, on 29 December and another to care@sulekha.com, the customer support id provided on its website, on 2 January. He didn’t receive any response.
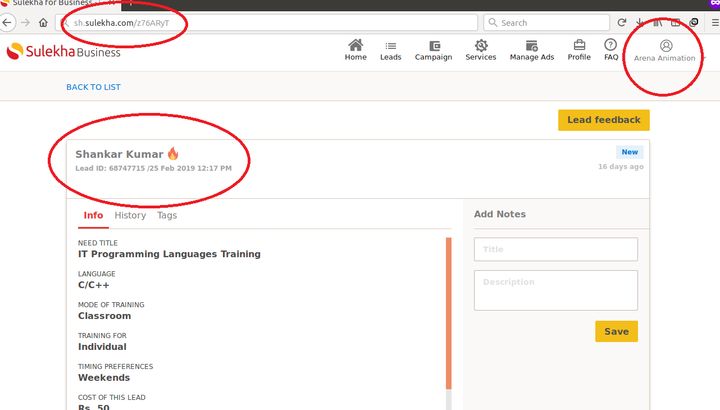
He then reached out to HuffPost India two months later, and demonstrated how the issue was still present through a new lead coming into his SMS inbox on 25 February. An Internet user searched on Sulekha for IT training institutes in Jalandhar around 12pm, and representatives of over a dozen registered companies offering this service got an SMS with the seven-digit code which would take them to their accounts, from where they could buy the customer’s contact details.
Entering the details in the Sulekha website, Singh typed ‘T’ instead of ‘V’ as the last character — and gained access to the account of a different IT training school in Jalandhar.
He could then view and edit personal information such as the name, address and contact details of the owner, as well as access the linked e-wallet and the entire transaction history of the company.
“Shocked, I further jumbled the entire seven-digit code, a mixture of numbers and alphanumeric characters, and managed to gain access into the profile of a Bengaluru-based computer education institute,” said Singh, who managed to view (and get editing rights to) the Sulekha accounts of over a dozen service providers.
The accounts also displayed scanned and uploaded documents such as driving licence, visiting card, e-Aadhaar, the company directors’ PAN cards and the Certificate of Incorporation issued by the Ministry of Corporate Affairs.
“The unique codes sent to me as a service provider around a year ago were also found working with the auto login option to view personal accounts of other service providers,” claimed Singh.
This is a concern because SMS-based authentication is now considered poor security. While it’s seen as better than nothing, experts now say you should be using authenticator apps, or other means of securing your accounts.
Dustin Maxey, Director of Product Marketing, Ping Identity writes: “Hackers can intercept SMS data via several methods that range in cost and complexity. The simplest and lowest-cost method for intercepting SMS messages is to use social engineering techniques to impersonate the authorized user. This may involve a telephone call, email exchange or online chat with a Customer Service representative, and indirectly changing the mobile phone number to an unauthorized phone. All MFA attempts using SMS will be sent to the new phone number. There may be no evidence that the phone number is not valid, and potentially insufficient notification to the authorized user, if any at all.”
Convenience versus security
Anyone who accessed another user’s account could also edit and replace the linked profile with their own without the service provider’s knowledge. This was made easier as Sulekha, instead of sending the OTP to the old phone number for verification, would send it to the new number added by the intruder, as verified by HuffPost India.
This would also allow the person to use the money in the company’s wallet.
“While the cost of a single lead is Rs 50, one has to first pay a minimum Rs 3,000 to activate Sulekha e-wallet,” added Singh.
However, logging into another’s user’s account would allow you to use their wallet money to buy the contact details of their leads, even if you didn’t have a wallet of your own.
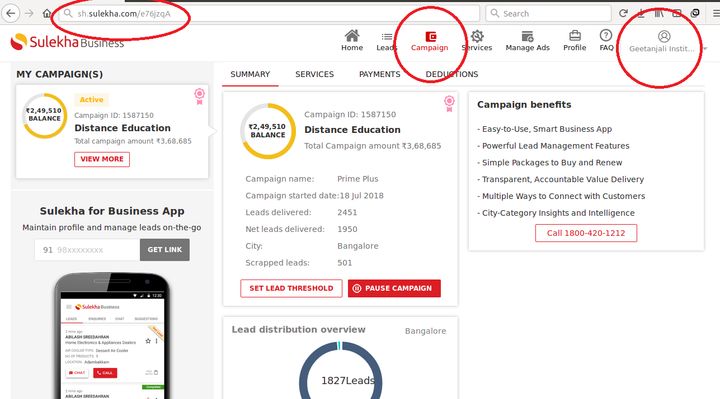
“We can view contact numbers of the leads and can call them directly to strike the deal without providing any information to the actual advertiser,” said Singh.
What’s more, the bug also allows you to view and read the chat history of the advertiser with its leads. One could change the media planning and the advertisement package bought by the service provider and even spend the entire amount in a single day without the advertiser’s knowledge.
Srini Vasan, Sulekha’s CTO, told HuffPost India that the URL to the ‘convenience’ feature was only sent to registered and verified customers to give them access to leads shared with their accounts. At the same time, he said that the company had recognised this as a potential issue and decided to remove the feature, but this only happened after HuffPost India contacted Sulekha.
“We figured out that few of our customers used to share the leads with their employees by just forwarding the SMS in order to pursue the leads. On understanding this user behaviour, we saw potential threats in data breach and made sure the URLs can be accessed only with the help of OTP,” claimed Vasan.
He, however, refused to admit the possibility of misuse of any customer account as any change to the accounts went through a manual verification process by his team.
However, this was not what was seen when testing the (now removed) feature. HuffPost India managed to make changes to Singh’s account (with his consent) through the auto login option.
Despite changing the owner’s name, adding new contact information and a few services to his personal account, Singh did not receive any alerts from Sulekha.