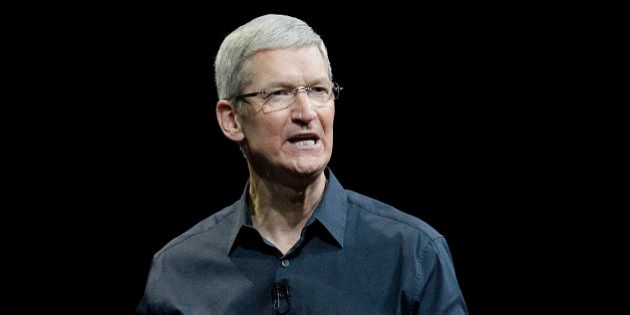
Apple CEO Tim Cook has written a strongly worded letter to customers about the importance of privacy, following the company’s decision to appeal a court order to unlock and access the data of an iPhone5c that belonged to Syed Farook, the terrorist who carried out the San Bernardino shooting along with his wife.
Apple, however, has openly refused to do so. Tim Cook’s letter also suggests that the FBI wants Apple to create a ‘backdoor’ in future iPhone releases and that this “threatens the security of our customers.”
The letter explains the need for encryption:
Smartphones, led by iPhone, have become an essential part of our lives. People use them to store an incredible amount of personal information… All that information needs to be protected from hackers and criminals…
Compromising the security of our personal information can ultimately put our personal safety at risk. That is why encryption has become so important to all of us.
For many years, we have used encryption to protect our customers’ personal data because we believe it’s the only way to keep their information safe. We have even put that data out of our own reach, because we believe the contents of your iPhone are none of our business.
Cook then goes on to explain the “dangerous” implications of the FBI’s request.
We have great respect for the professionals at the FBI... Up to this point, we have done everything that is both within our power and within the law to help them. But now the U.S. government has asked us for something we simply do not have, and something we consider too dangerous to create. They have asked us to build a backdoor to the iPhone.
Specifically, the FBI wants us to make a new version of the iPhone operating system, circumventing several important security features, and install it on an iPhone recovered during the investigation. In the wrong hands, this software — which does not exist today — would have the potential to unlock any iPhone in someone’s physical possession.
The FBI may use different words to describe this tool, but make no mistake: Building a version of iOS that bypasses security in this way would undeniably create a backdoor. And while the government may argue that its use would be limited to this case, there is no way to guarantee such control.
He then explains the “chilling” consequences that might result from complying with the government’s orders, or what he terms as “overreach”.
The implications of the government’s demands are chilling. If the government can use the All Writs Act to make it easier to unlock your iPhone, it would have the power to reach into anyone’s device to capture their data. The government could extend this breach of privacy and demand that Apple build surveillance software to intercept your messages, access your health records or financial data, track your location, or even access your phone’s microphone or camera without your knowledge.
Opposing this order is not something we take lightly. We feel we must speak up in the face of what we see as an overreach by the U.S. government.
Apple is known to be a strong votary of customer data security and encryption and has emphasized its stance in every product launch. From iOS8, all the data on the disk of an iPhone is strongly encrypted. Ben Thompson of Startechary has given a great technical breakdown of the encryption system in the iPhones and what FBI is asking for in a blog post.
The whole tech industry rallied behind Tim Cook to support encryption on devices and the personal security of the users.
Renowned whistleblower Edward Snowden said in a tweet, Citizens should be relying on FBI for security rather than Apple, not the other way around.
The @FBI is creating a world where citizens rely on #Apple to defend their rights, rather than the other way around. https://t.co/vdjB6CuB7k
— Edward Snowden (@Snowden) February 17, 2016
WhatsApp CEO Jan Koum voiced his support to Tim Cook in a Facebook post.
Google's CEO Sundar Pichai stated the importance of encryption in five tweets.
1/5 Important post by @tim_cook. Forcing companies to enable hacking could compromise users’ privacy
— sundarpichai (@sundarpichai) February 17, 2016
2/5 We know that law enforcement and intelligence agencies face significant challenges in protecting the public against crime and terrorism
— sundarpichai (@sundarpichai) February 17, 2016
3/5 We build secure products to keep your information safe and we give law enforcement access to data based on valid legal orders
— sundarpichai (@sundarpichai) February 17, 2016
4/5 But that’s wholly different than requiring companies to enable hacking of customer devices & data. Could be a troubling precedent
— sundarpichai (@sundarpichai) February 17, 2016
5/5 Looking forward to a thoughtful and open discussion on this important issue
— sundarpichai (@sundarpichai) February 17, 2016



Contact HuffPost India
